For cybersecurity professionals, there are a handful of common security frameworks (CSFs) that can be utilized to categorize risk, identify applicable controls, assess current compliance, and provide a roadmap to implement and sustain a healthy program. Commonly used frameworks include NIST, SOC2, HITRUST, and ISO 27001 just to name a few. For U.S. Federal agencies, the more rigid structure of NIST makes it the prescribed framework and a legal requirement via Federal Information Security Modernization Act (FISMA). SOC2 isn’t legally required but is often the choice for service providers and vendors who process, store, and transmit sensitive customer data. HITRUST is the highly recommended choice for companies handling sensitive health information (PHI). That leaves us with ISO 27001 or as I frame it (pun intended), the framework for the rest of us. Why? The answer lies ahead.
ISO 27001: The Basics
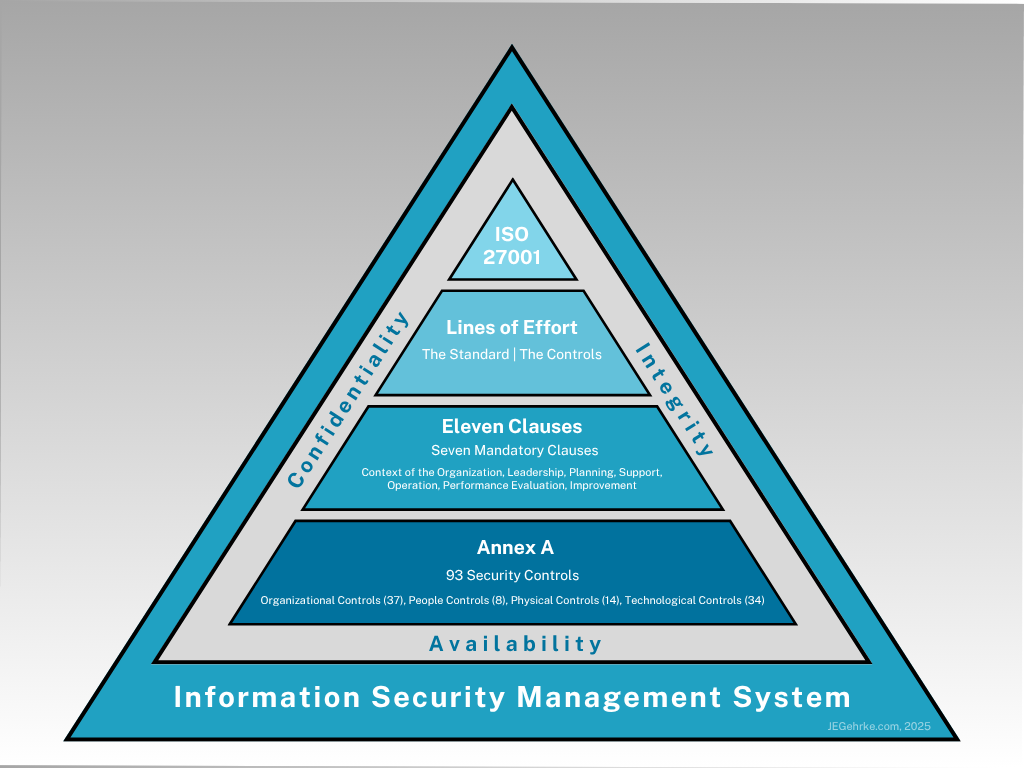
Created and maintained by the International Organization for Standardization (ISO), ISO 27001 was first published in 2005, with its roots coming from the British Standard BS 7799-2. From the initial version to the most recently published 2022 version, the intent was and is to provide a structured framework to identify, assess, and manage risk to and, residually, implement and sustain an Information Security Management System (ISMS). An international standard, I characterize it as a framework for the rest of us because it isn’t only U.S.-focused and can be used regardless of business size or type. It’s also more user-friendly and flexible than more rigid ones like HITRUST and NIST. Additionally, ISO 27001 is a set of voluntary guidelines and best practices. It should be noted, though, that many companies require their service providers, vendors, or partners to be certified in the framework. The graphic below illustrates the ISMS structure with ISO 27001 as the standard.
Now that we’re all up-to-speed on the basics, we can move forward to a look at the pros and cons of the framework. Review and analysis of them in relation to our network type, composition, mission, etc. will tell us if our organization falls into the “rest of us” category.
ISO 27001: The Pros
- Enhanced Security Posture: ISO 27001’s structured framework framework allows for identification, assessment, and management of information security risks. Fewer risks translate into reduced probability of falling victim to cyberattacks and data breaches.
- Stakeholder Trust: Implementing ISO 27001 and achieving certification in it proves to customers, partners, and investors that the organization is committed to security and knows how to do it.
- Regulatory Compliance: As mentioned above, it’s a voluntary framework. As also mentioned, though, being ISO 27001 certified means being able to demonstrate compliance with legal and regulatory requirements like GDPR, HIPAA, etc., in whatever our organization’s industry or country location is.
- Improved Business Continuity: As mentioned, ISO 27001 empowers an organization to have an enhanced security posture. From a business perspective, implementation of a formal cybersecurity structure, baseline standardization, and uniformly applied policies and procedures means both technical and non-technical personnel are better prepared to sustain essential functions during technical disruptions. Continuity capability also serves to increase the stakeholder trust mentioned above.
Other pros on which I won’t go into detail include increased competitive advantage, operation and maintenance cost-savings, and greater cybersecurity awareness across the organization. For any seasoned technology professional, they’re pretty self-explanatory.
ISO 27001: The Cons
- Financial Investment: Organizations without in-house cybersecurity support means a costly payment to have a vendor do it for you. Having a dedicated cybersecurity staff means you may be able to implement ISO 27001, but in both scenarios obtaining formal certification requires paying a qualified vendor. In an in-house scenario, there also may be costs associated with hiring consultants and sending staff through formal training. In most cases, these costs aren’t realistic for small to medium-sized organizations.
- Resource Intensity & Complexity: While the framework its more flexible than others, that doesn’t mean it’s a quick or easy process to plan and execute. It should be treated like any other technology project, with a project lead, development of an actual plan, and continuous oversight. Additionally, the project team should receive formal training to prior to trying to take it on. The only scenario in which I could recommend just reading the manual and going for it is if you have veteran cybersecurity staff with in-depth experience in one or more of the other common frameworks. The order and method of operation may be different with ISO 27001, but the back-end actions and procedures to implement it are generally the same.
For me, these two cons are the most impactful ones to consider if opting for ISO 27001. What are other cons you may need to be consider? Some would opine that the bureaucratic overhead of developing and updating the many, many documents needed to support and evidence control implementation is too much. Additionally, ISO 27001 requires dedicated focus and the continuous monitoring required to maintain it can be difficult without a super-sized cybersecurity staff.
ISO 27001: The Take-away
This is a high-level view of the framework, but hopefully it gives enough information to determine if it’s worth pursuing in your organization. As with all frameworks, you get out of it as much as you put into it. If you do pursue it, commit fully, do your research, make your project plan, and stick to it. One thing that’s guaranteed is that there will be staff members who don’t like it. It’s new. It’s uncomfortable. It requires critical thinking. Change is admittedly difficult, but if you market it to the staff correctly and positively involve people, they’re much more likely to embrace it. It may feel painful up front, but the enhanced cybersecurity posture on the back end makes it worth the effort. After all, the overarching idea behind any CSF is to make the organization’s network, systems, and data more secure. Whether it’s ISO 27001 or another flavor, your framework of choice is the cornerstone in building the cybersecurity culture of compliance that I’ve spoken of in the past, and the organization’s enhanced cybersecurity posture on the other side will only make your culture flourish even more.

